libc进阶之LitCTF_2024

不同的libc版本,但是源码是相同的
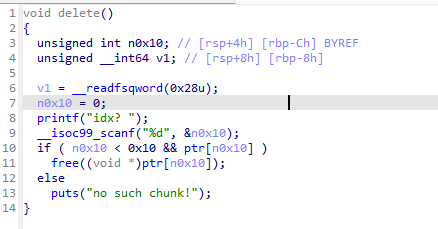
delete 有uaf漏洞
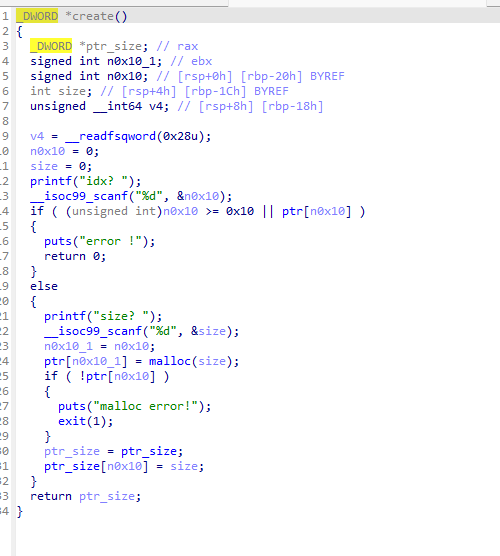
create
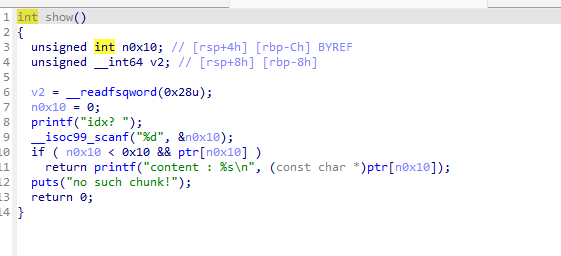
show
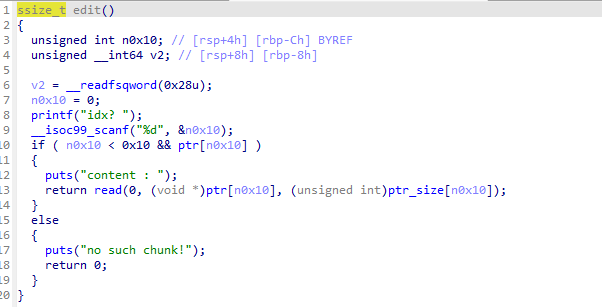
edit
2.23
uaf漏洞,打fast bin攻击就好
1 | from pwn import * |
2.27
从 glibc 2.26 开始引入 tcache(Thread Cache)
只检测 连续两次 free 同一个 chunk。
tcache / fastbin 存的是 user chunk 指针
unsorted / small / large 存的是 chunk header 指针
tcache刚出来,还没有什么校验,直接覆盖tcache bin的fd,把chunk创在free_chunk处并覆盖为system函数就好
1 | from pwn import * |
2.31
tcache double free 检查更强了,它会在对应 size 的 tcache bin 里遍历整条链,检查这个 chunk 是否已经在链里。
safe-linking (fd = next ^ (heap_base >> 12))是 2.32 才加的。
把tcache的7个槽填满,然后再free一个unsorted bin泄露libc,之后改最后一个槽的fd,让malloc到free_hook
执行后门函数
1 | from pwn import * |
2.35
彻底删除 __free_hook 和 __malloc_hook (2.34+)
引入 Safe-linking 机制 (2.32+)
对IO结构体下手,house of apple,由于前不久才总结过,所以这里只给出脚本
具体的调试分析可以看house of apple
1 | from pwn import * |
2.39
没有革命性改变,但是基础防护更严格了
house of apple还可以使用,大门时malloc的大小被限制为large bin,把间隔的chunk改大就好
1 | from pwn import * |
